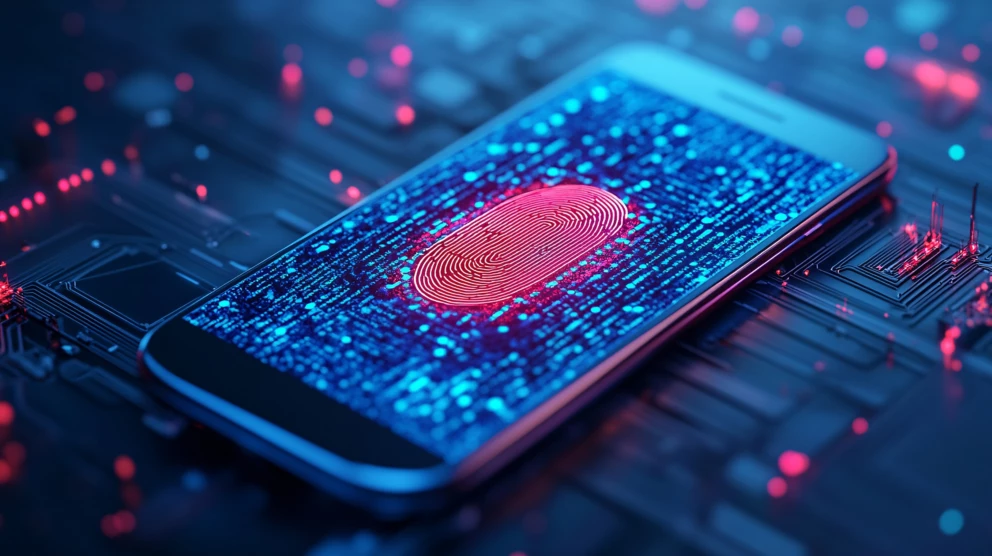
Imagine a world where hackers fall into their traps. In the ever-evolving landscape of cybersecurity, one concept has gained traction for its deceptive brilliance: h0n3yb33p0tt. But what exactly is it?
The nature of H0n3yb33p0tt remains unclear because it functions as a protective cybersecurity measure and is potentially an advanced weapon in digital warfare.
This article examines H0n3yb33p0tt’s fundamental character, operation fundamentals, and value while explaining why cybersecurity experts and businesses use it for threat detection and elimination.
What is H0n3yb33p0tt?
H0n3yb33p0tt represents the current version of honeypot technology, which exists as a security mechanism to deceive cyber attackers through artificial interfaces. Honeypots actively participate with threats through simulated targets, whereas passive security tools rely on defensive measures only.
Therefore, organizations can obtain insights and intelligence into hacking techniques, which assists their security enhancement process.
H0n3yb33p0tt’s key features and functionalities include:
- Sophisticated Threat Detection: Using signature-based, anomaly-based, and policy-based detection methods, H0n3yb33p0tt’s advanced algorithms identify many cyber threats within its decoy environments, from basic scans to sophisticated attacks like APTs. This layered approach ensures comprehensive threat coverage.
- Real-Time Monitoring and Alerts: H0n3yb33p0tt monitors real-time activity and provides immediate alerts upon threat detection. The system analyzes interactions, logs attack strategies, and notifies administrators, enabling rapid response and mitigation of potential damage.
- Seamless Integration: H0n3yb33p0tt integrates smoothly with existing security systems, such as SIEM, intrusion detection systems, and other cybersecurity frameworks. This integration enhances existing tools with additional security layers and enriched data for improved threat analysis.
How Does It Work?
At its core, H0n3yb33p0tt operates as a decoy system, mimicking real networks or applications. When hackers attempt to breach the system, they unknowingly engage with a controlled environment that logs their actions, methods, and tactics. This intelligence helps cybersecurity teams understand vulnerabilities and reinforce their actual systems.
The Influence on Online Culture:

H0n3yb33p0tt has had a profound influence on various aspects of online culture. One of the most notable impacts is how the persona interacts with internet trends and subcultures. It taps into the world of memes, fan communities, and digital art, giving voice to a generation deeply immersed in digital expression.
The persona has also played a pivotal role in shifting the narrative around online identity. Whereas many digital identities are created for specific purposes—such as gaming or socializing—H0n3yb33p0tt blurs the lines between these realms.
The character’s fluidity across different platforms and contexts reflects the evolving nature of digital interactions. Today, many internet users adopt multifaceted online identities, and H0n3yb33p0tt exemplifies how these personas can transcend traditional boundaries.
Read More: Dealasty-Simplify Your Experiences
H0n3yb33p0tt, while powerful, faces potential challenges and limitations:
- Advanced Attacker Detection: Despite its efforts to remain undetected, H0n3yb33p0tt will find it hard to keep advanced attackers away from its traps. Ongoing development and refinement of honeypot technologies are essential to stay ahead of these advanced threats.
- Resource Management: While generally less resource-intensive than some security solutions, H0n3yb33p0tt still requires careful resource allocation. Proper implementation is essential to prevent the honeypots from burdening or negatively impacting network performance and security.
H0n3yb33p0tt in Gaming and Online Communities:
In gaming, h0n3yb33p0tt serves as a player’s identity, helping them stand out in multiplayer environments. Its creative structure fits well within online subcultures, fostering community-building among like-minded individuals. It also plays a key role in branding streamers and esports players.
H0n3yb33p0tt offers valuable applications across various sectors:
1. Business Environments:
In corporate settings, where data protection is critical, H0n3yb33p0tt enables a proactive security strategy. The tool identifies and reacts to ransomware threats against company networks to stop damaging situations from intensifying.
2. Research and Development:
The powerful analytical tool H0n3yb33p0tt supports research about cybersecurity at its highest level. Research in this protected environment enables scientists to understand new attack methods and create better security measures.
3. Educational applications:
It introduces H0n3yb33p0tt into educational applications for teaching students hands-on cybersecurity skills. By interacting with this advanced honeypot, students gain valuable skills in threat detection, network security monitoring, and proactive cybersecurity practices.
Read More: www gravityinternetnet-The world behind
The Role of H0n3yb33p0tt in Modern Cybersecurity:
1. Threat Intelligence Collection:
The most significant benefit of H0n3yb33p0tt comes from its capability to produce immediate data analysis of cyberattacks. Organizations gain access to analysis abilities for attack vectors, malware behaviour, and hacker strategic insights to predict future threats.
2. Reducing False Positives:
Ordinary security systems create massive numbers of alerts, many of which prove useless because they are simply false detections. H0n3yb33p0tt functions as a honeypot that specifically targets genuine threats so security staff can prioritize actual dangers.
3. Strengthening Defensive Strategies:
Removing honey traps by security professionals lets them understand hacker movements so they can identify system flaws in time before hackers exploit them through actual cyberattacks.
4. Legal & Ethical Cyber Defense:
Using H0n3yb33p0tt allows organizations to track cybercriminal activities without violating privacy laws. Since hackers voluntarily engage with the decoy system, businesses can monitor their tactics without ethical concerns.
The Future of H0n3yb33p0tt:
As we look ahead, the Future of H0n3yb33p0tt appears bright. The character succeeds because it learns fresh digital skills and connects with new technology while keeping up with internet trends forever. Through different methods, H0n3yb33p0tt is a major participant in online activities.
Read More: Mansrufer-Redefining Digital Innovations and Customer Experience
FAQs:
1. What is H0n3yb33p0tt known for?
The persona creates unique web content mixed with digital media and provides social viewpoints about mental wellness and self-acceptance.
2. How does H0n3yb33p0tt influence online culture?
The impact h0n3yb33p0tt makes on online culture arises from mixing creative activities with popular culture and activism, bridging internet communities between games, social media, and digital creations.
3. Is H0n3yb33p0tt involved in gaming?
Yes, H0n3yb33p0tt is an active member of gaming communities, streaming on platforms like Twitch and engaging with fans through multiplayer games.
Conclusion: Why H0n3yb33p0tt Matters:
Cybersecurity requires constant effort, and H0n3yb33p0tt is a strong defence tool against cyber criminals. By managing attacks in a protected area, the program teaches hackers what to do and how to protect systems better.